One of the biggest takeaways we've learned from 2022 is that many organizations aren’t aware of the explosion in cybersecurity threat frequency and severity that has taken place over the past year.
Some organizations may have IT staff in place to handle cybersecurity threats, but they have no way of knowing if their defences are strong enough to withstand the new challenges that 2023 will bring.
We've compiled a list of our Top 10 articles that your organization needs to read to get ready for 2023.
Top 10 MUST-READ Articles
#1 Evolving Lottery, Evolving Risk
Lottery operations are constantly changing and evolving. That’s why it’s critical to stay informed.
One of the most pressing cybersecurity threats facing the lottery industry today is Ransomware-as-a-Service. Cybercriminals can now purchase everything they need to execute a successful ransomware attack for less than $100. Considering the average ransom demand climbed to over $200,000 in 2021, you can see why it is an attractive investment.
Our VP of Information Security Services, Gus Fritschie, shares his insights from 2022, along with three key challenges that lotteries are facing today.

#2 Embracing and Learning from a Cyber Insurance Application
When gaming organizations plan to invest or renew an insurance policy, it’s becoming more common for insurance providers to send a cyber insurance application with the goal of better understanding the customer’s security posture and risks.
With that, who is responsible for completing the application within a company? Is it the IT department, legal counsel, compliance, human resource, or senior executives? The answer: everyone. It’s everyone’s role to contribute and understand the importance of cybersecurity, what measures are currently in place, where the risks are, what the impacts are, etc.
Our VP of Business Development answers these questions in her article, Embracing and Learning from a Cyber Insurance Application.

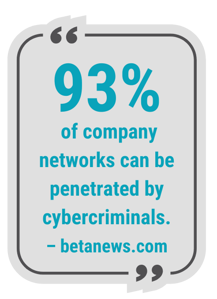
#3 The Rise of the Cybercrime Gig Economy
Stolen credentials are a goldmine for threat actors. Why would a hacker try to break into your network when they can simply log in?
You may not become aware of a stolen digital identity for quite some time because:
▪ The attacker will create a backdoor account to provide permanent access into your network, and then “rent out” that access to whoever is willing to pay.
▪ Lower-value credentials might be listed for bulk sale on the dark web.
▪ The attacker might “camp out” in your network, sending malicious messages to your trusted contacts to farm more victim leads that they can then turn around and sell or collect other types of data to enable a more widespread attack.
Learn more about how the cybercrime economy is growing and how you can protect your organization in our latest article, The Rise of the Cybercrime Gig Economy:
.png?width=231&height=462&name=93%25%20(1).png)
#4 How Forced Hybrid Work Created Vulnerable Businesses
 As the dust settles after the largest public health crisis of our life, many businesses are realizing they are never going back to “normal.”
As the dust settles after the largest public health crisis of our life, many businesses are realizing they are never going back to “normal.”
Instead, most organizations have concluded that instead of a full-time return to the office, a hybrid workplace is the best way forward. They're also learning that this new hybrid working model has its own challenges — particularly when it comes to IT security.
Learn what your organization should know about working in a hybrid environment:
#5 What Business Leaders Need to Know About Cybersecurity Going into 2023
Cyberattacks have increased by 400% compared to pre-pandemic times. Is Your business prepared?
Running a business requires leaders to hold a comprehensive skill set and cybersecurity expertise isn't necessarily on that list. However, the reality is that cybersecurity is no longer simply an issue for your IT team. This eBook can help you understand modern cyberthreats and their potential impact on your business.
#6 Building the Business Case for an Outsourced Security Operations Centre
If this describes the situation you’re in today, you’re not alone. Cyberattacks have increased 400% compared to pre-coronavirus time. The increase combined with the fact that many mid-size businesses do not have any cybersecurity plan in place at all means most organizations are in big trouble.
.jpg?width=5760&height=3840&name=Bulletproof%20SOC%20(1).jpg)
#7 Municipalities Need to Prepare for Data Breaches

#8 What does the Consumer Privacy Policy mean for Microsoft Customers
The proposed Consumer Privacy Policy closes a number of privacy gaps that existed in the previous PIPEDA legislation and introduces stricter standards for data governance and control. It also implements a new Personal Information and Data Protection Tribunal that has much greater power to enforce rules and levy fines and other sanctions against organizations that fail to comply.
Although the proposed new rules must still work their way through the legislative process, it is likely that Canadian businesses will need to comply with stricter data protection laws in the next year or two.
Read this article to learn the most significant changes proposed by CPPA and how they could affect Microsoft customers that collect and use consumer data:
.png?width=200&height=250&name=Copy%20of%20Constant%20Contact%20Email%20Graphic%20(1).png)
#9 What Today’s Explosion in Cybercrime Means for your Small Business
A misconception that many organizations have is that hackers are not interested in targeting small businesses. The opposite is true.
58% of security breaches happen to small businesses, and many don't have the resources to survive the financial and reputational damage a breach may cause. Hackers continuously monitor the entire market for areas of vulnerabilities and often target smaller companies precisely because they know those businesses have underinvested in cybersecurity.
It’s also worth considering that cybercriminals will bring the same level of sophistication to attacking an SMB company as they do a large Fortune 500 enterprise—and because the first phase of the hacking process is automated, they will come at your company just as hard.
#10 How Bulletproof Helped the City of Saint John Overcome a Ransomware Attack and Strengthen Their Security Posture
 If you received a call at 11 PM stating your organization had been targeted by a ransomware attack demanding approximately $12-14M, what would you do? Would your team be ready? 🤔
If you received a call at 11 PM stating your organization had been targeted by a ransomware attack demanding approximately $12-14M, what would you do? Would your team be ready? 🤔
Learn how the City of Saint John jumped into action, refused to pay the ransom demand, and built a stronger network for the city with the help of their team, Bulletproof, and the support of Microsoft Security solutions.
Get Bulletproof Expertise
We're here to help solve your cybersecurity problems.
Complete the form and we'll connect you with our cybersecurity experts.
![Microsoft Partner of the Year [POTY] Logo_White Transparent Microsoft Partner of the Year [POTY] Logo_White Transparent](https://content.bulletproofsi.com/hs-fs/hubfs/Microsoft%20Partner%20of%20the%20Year%20%5BPOTY%5D%20Logo_White%20Transparent.png?width=1624&name=Microsoft%20Partner%20of%20the%20Year%20%5BPOTY%5D%20Logo_White%20Transparent.png)









