Cyberattacks against municipalities at the local and state level have increased by 50% over the past five years. This is because the wealth of information state and local governments possess make them prime targets for cybercriminals looking to gain access to government operations, and citizens and their activity. Politized attacks by nation-state actors have made news headlines but these threats aren’t just felt at a federal level. With the Biden administration’s recent announcement of more than $1 billion in federal cybersecurity funding over the next four years, and an explosion of cybercrime since the Covid-19 pandemic, there has never been a better time to look at your eligibility—and your cybersecurity posture.
With decades of technology, security, and compliance experience, we know how important strategic investment in cybersecurity is, and how damaging a situation can get should a cyberattack occur for state, local, and territorial government entities. Bulletproof was recently awarded with a GSA Multiple Award Schedule. As a Highly Adaptive Cybersecurity Services (HACS) holder, you can trust the strong cybersecurity and IT work that our team is conducting across the U.S. and around the globe.
Article Sections

Awarded GSA Multiple Award Schedule
The GSA Multiple Award Schedule Program is the government’s premier commercial product and service contracting program. For a contractor to be awarded a Multiple Award Schedule (MAS), they must comply with strict regulations and policies. Organizations granted a GSA designation can sell products and services directly to US government agencies at pre-negotiated pricing.
Key Trends in Cybersecurity Landscape
Here are the key trends that we’re monitoring in the cybersecurity landscape that serve as perfect reasons to research available grants and carve out resources for establishing governance, identifying vulnerabilities, implementing mitigation measures, and working to develop a strong cybersecurity workforce.
1. Rise of Ransomware & Cyberthreats
“Cyberattacks have emerged as one of the most significant threats to our homeland,” says Secretary of Homeland Security Alejandro N. Mayorkas; and he’s not wrong. Through the cybercrime gig economy ransomware is now available for purchase as a service, meaning bad actors can purchase everything they need to infiltrate your organization and hold your data for ransom as easily as they can order takeout.
These attacks are threatening schools, healthcare, even state governments and federal elections—and cybercriminals show no sign of slowing down. It is important to be prepared in the event of an attack, and you can start by asking yourself two mission-critical questions: Has your company evaluated its existing incident response protocols? How are you prepared to recover from an cyberattack?
![]()
The FBI has reported a 400% increase in cyberattacks compared to pre-pandemic times.
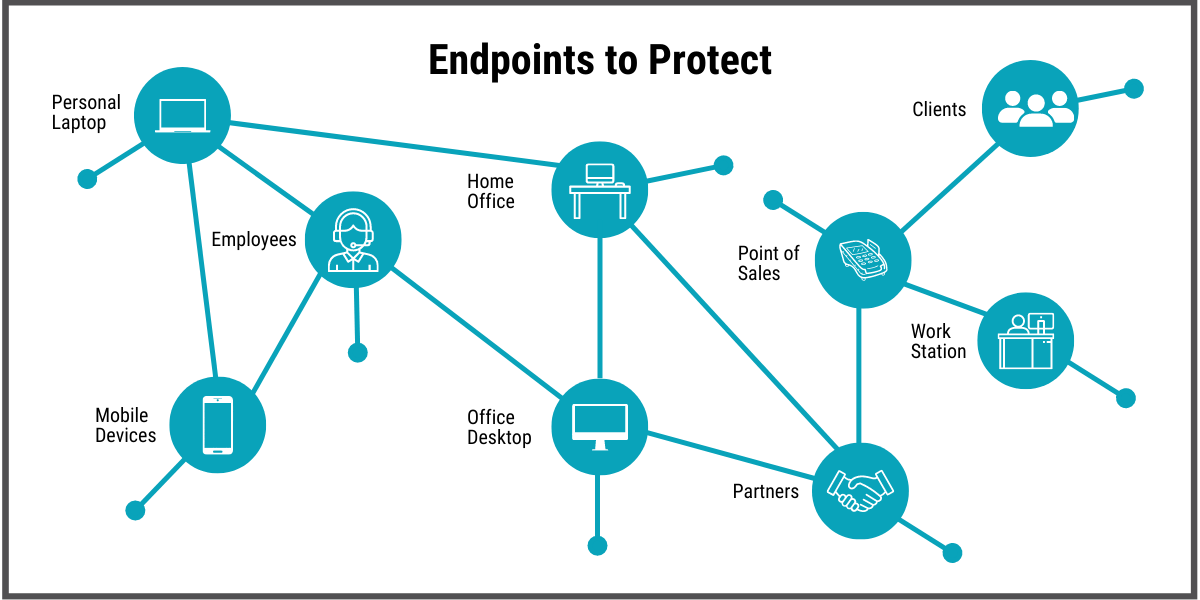
2. Remote Work & Endpoints Everywhere
The hybrid work trend isn’t going away and as state, local, and territorial government workforces become more remote and distributed, many more potential points of vulnerability are being generated.
By configuring your technology for remote work, you’re expanding your perimeter and increasing your security risk and attack footprint—especially if the transition is not properly implemented. Now that your workers and systems are no longer confined within walls, access control and secure remote solutions are critically important. It is crucial that you spend time evaluating the security of your cloud tenants (because cybercriminals certainly are!)
3. Ever-Evolving Federal & State Cybersecurity Regulations
We are seeing a higher focus placed on security requirements in the form of federally-and state-mandated security standards. These mandated requirements recognize the landscape’s growing threat and strive to protect data privacy and security, as well as cybersecurity transparency. Some of these federally mandated regulations include Cybersecurity Maturity Model Certification (CMMC) and Minimum Acceptable Risk Standards for Exchanges (MARS-E). While there are organizations to support the development of these higher standards of security and compliance and those seeking to achieve them—like the National Institute of Standards and Technology (NIST) and the International Organization for Standardization (ISO)—there’s no denying that an investment of time and resources is necessary to excel in areas of regulations and compliance.
The State and Local Cybersecurity Grant Program (and the forthcoming Tribal Cybersecurity Grant Program) can be the backbone of your future plans to fortify your cybersecurity and the basis of projects rooted in regulatory requirements. Don’t be overwhelmed by increased regulations; trusted cybersecurity vendors and partners are here to help ease the burden and provide support.
4. The IT & Cybersecurity Skills Gap
It has never been more challenging to fill an IT position, nor more important to have an all-star team on your roster to shore up your defenses against cyber threats. An increased need for qualified personnel combined with a skills gap in the workforce places a greater burden on existing IT teams. Establishing relationships with trusted vendors is one answer to this problem. An integrated, automated security stack and outsourcing IT projects and security operations are others.
Don’t let the pace of change and increase in threat when it comes to cybersecurity overwhelm you. Support is there. Learn more about available cyber grants and reach out to discuss how Bulletproof can partner with you to support you on your journey to cybersecurity.
![]()
Bulletproof Credentials
- Bulletproof named to CRN's Managed Services MSP 500 List for 2026
- Bulletproof named to CRN's Managed Services MSP 500 List for 2025
- 2025 Microsoft Intelligent Security Association Excellence Award Finalist, Security Trailblazer
- 2025 Municipal Information Systems Association BC - Associate Partner of the Year
- 2024 Microsoft Intelligent Security Association Excellence Award Winner, Security Trailblazer
- 2021 Global Security Partner of the Year Winner, Microsoft
- 5X Microsoft Canada Security IMPACT Award Winner
- 20+ years of IT, security, & compliance knowledge serving various industries across North America
- Global state-of-the-art 24/7 Security Operations Centers (SOC), 24/7 Service Desk Support, Network Operations Center (NOC), & Technology Operations Center (TOC)
-
Long-standing Microsoft Solutions Partner for Modern Work, Digital & App Innovation Azure, Infrastructure Azure, Data & AI, and Security with specializations in Cloud Security, Identity & Access Management, Data Security, and Threat Protection.
-
Member of the Microsoft Intelligent Security Association
-
Awarded General Services Administration (GSA) Multiple Award Schedule (MAS) with holder of Highly Adaptive Cybersecurity Services (HACS)
-
Certified Cybersecurity Maturity Model Certification (CMMC) Practitioner Organization

Vasu Jakkal, CVP, Microsoft Security
Book Your Complimentary Cybersecurity Consultation
We're here to help solve your complex IT and security problems.
Get in touch by completing this form and we'll connect you with a Bulletproof expert.


![Microsoft Partner of the Year [POTY] Logo_White Transparent Microsoft Partner of the Year [POTY] Logo_White Transparent](https://content.bulletproofsi.com/hs-fs/hubfs/Microsoft%20Partner%20of%20the%20Year%20%5BPOTY%5D%20Logo_White%20Transparent.png?width=1624&height=594&name=Microsoft%20Partner%20of%20the%20Year%20%5BPOTY%5D%20Logo_White%20Transparent.png)
