Identifying and protecting Sensitive Data at Enterprise Scale
Cybersecurity is a constantly shifting landscape. As our digital world continues to grow, so do the risks. Currently the top three data security concerns are:
- Data security incidents are more common than the headline news. Organizations on average experience 59 data security incidents with 20% being severe.
- Business value can be lost due to poor data security. 74% of organizations have had a business data exposed in the past year
- A fragmented solution landscape can weaken security posture. Organizations that use 16 or more security tools experience 2.8X more data security incidents
Source: Data Security Index, Microsoft, 2023
Data security incidents can happen anytime, anywhere
With more than 300 million people working remotely all over the world and collaborating across multiple environments and devices, data security incidents can happen anytime anywhere.
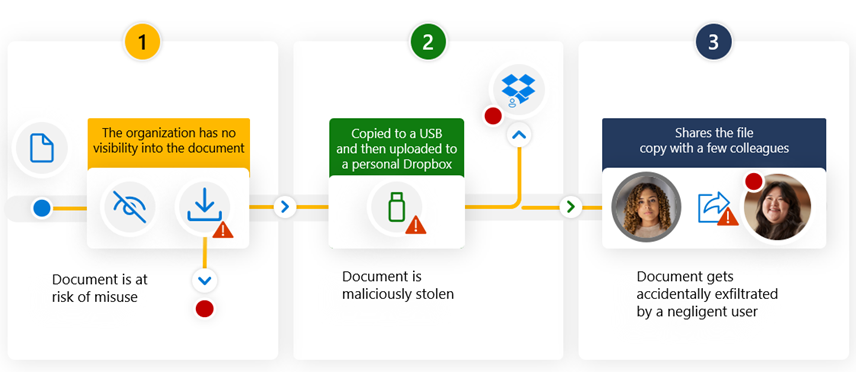
There are three primary scenarios for data security incidents:
- If your organization doesn't have visibility into it's data – the data is at risk of misuse (exfiltration, exposure, etc.)
- If a user has malicious intent and is trying to exfiltrate the data
- If a user inadvertently takes a sensitive document and makes it visible.
What Organizations Need To Do
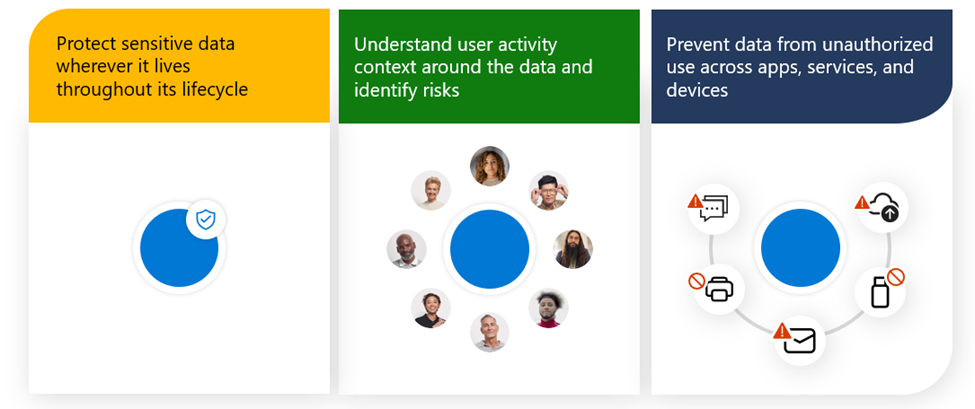
To help address the data security challenges, organizations need to implement multiple controls, including preventing data from unauthorized use across workloads, protect sensitive data wherever it lives throughout its lifecycle, and understand user activity context around the data. You need to do all three to fortify your data security strategy, and we can help.
Fortify data security with an integrated approach
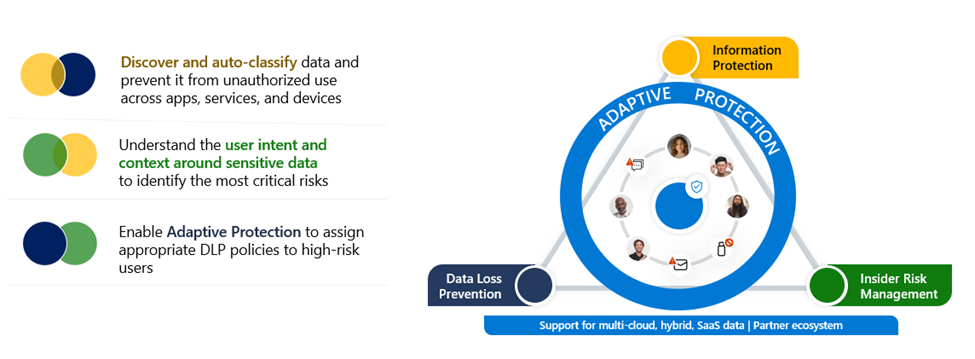
You need all three defenses of protection to effectively secure data from potential data security incidents and they work better together with reinforced synergy across the platform.
For example, if you use Information Protection and Data Loss Prevention together, you are able to discover and auto-classify the data and prevent it from unauthorized use. Using Information Protection and Insider Risk Management together, you can understand the user intent around sensitive data to identify the most critical data risks in your organization.
Another example is if you use Insider Risk Management and Data Loss Prevention, then you can enable Adaptive Protection which assign appropriate DLP policies based on user’s risk levels. We will explain more about Adaptive Protection in the next slide. If you use all three products, then you can fortify your data security with a defense-in-depth approach.
What Organizations Need to Ensure Data Security
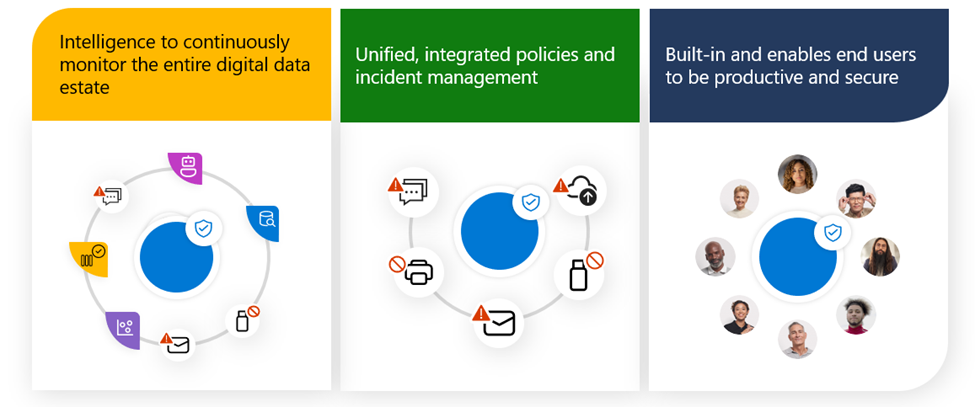
So, what’s needed for data security? We see three primary pillars. The first is intelligence to drive continuous discovery and monitoring for sensitive data to allow you to understand where sensitive data is stored in your data estate as well as how it is being used.
Next is the ability to leverage unified and integrated policies so that data ex-filtration can be protected across all egress channels across all locations. Coupled with this is our unified incident management and remediation capabilities that bring together signals that can be intelligently correlated across multiple risk vectors for the SOC or DLP analysts.
And finally, data security needs to be built-in and enable end-users to securely collaborate with others without impacting their productivity. Let us walk through each pillar and go over the powerful capabilities that can help you achieve your data protection goals.
Bulletproof Your Microsoft
Bulletproof offers a comprehensive suite of cybersecurity services designed to meet the unique needs of your organization. By consolidating vendors and leveraging Bulletproof’s expertise, you can achieve robust security while reducing costs and complexity.
Key Features of Bulletproof Cybersecurity Services
- Integrated Security Platform: Bulletproof provides a unified platform that integrates seamlessly with existing systems, reducing security gaps.
- Advanced Threat Detection and Response: Utilizing extended detection and response (XDR) technologies, Bulletproof ensures rapid identification and mitigation of threats.
- Compliance and Certification: Bulletproof helps you comply with stringent standards, including CMMC, HIPAA, NIST, and ISO.
- Managed Security Services: Continuous monitoring and management of security systems provide ongoing protection and peace of mind.
- Comprehensive Support: From consulting to implementation and beyond, Bulletproof offers end-to-end support.
Are you ready to streamline your cybersecurity efforts and enhance your operational efficiency? Partner with Bulletproof to leverage our integrated, best-of-platform approach and ensure your organization’s processes are secure and efficient.
Next Steps

Make Your Business Immune to Disruption with Our Security Operations Center
Did you know that there are 1.7 million ransomware attacks every day? That’s 19 every second! If that number doesn’t alarm you, consider this: the average cost of a ransomware attack is a staggering $1.85 million!
That’s where our Security Operations Center (SOC) comes in. Our SOC is dedicated to serving and protecting our customers around the clock, providing 24/7 protection no matter where you are.
Watch this video for an exclusive inside look at how we keep your business secure.
.png?width=496&height=279&name=MSFT%20Ignite%20Resource%20Thumbnails%20(1).png)
Microsoft Data Security Envisioning Workshop
Identify data security risks in your organizational data.
As your business-critical data expands and your workforce shifts to remote work, having an integrated approach that can help quickly identify, triage, and act on data security risks is more important than ever.
Bulletproof Credentials
- Bulletproof named to CRN's Managed Services MSP 500 List for 2026
- Bulletproof named to CRN's Managed Services MSP 500 List for 2025
- 2025 Microsoft Intelligent Security Association Excellence Award Finalist, Security Trailblazer
- 2025 Municipal Information Systems Association BC - Associate Partner of the Year
- 2024 Microsoft Intelligent Security Association Excellence Award Winner, Security Trailblazer
- 2021 Global Security Partner of the Year Winner, Microsoft
- 5X Microsoft Canada Security IMPACT Award Winner
- 20+ years of IT, security, & compliance knowledge serving various industries across North America
- Global state-of-the-art 24/7 Security Operations Centers (SOC), 24/7 Service Desk Support, Network Operations Center (NOC), & Technology Operations Center (TOC)
-
Long-standing Microsoft Solutions Partner for Modern Work, Digital & App Innovation Azure, Infrastructure Azure, Data & AI, and Security with specializations in Cloud Security, Identity & Access Management, Data Security, and Threat Protection.
-
Member of the Microsoft Intelligent Security Association
-
Awarded General Services Administration (GSA) Multiple Award Schedule (MAS) with holder of Highly Adaptive Cybersecurity Services (HACS)
-
Certified Cybersecurity Maturity Model Certification (CMMC) Practitioner Organization

Vasu Jakkal, CVP, Microsoft Security
Get Bulletproof Expertise
By 2025, 60% of organizations will be actively using remote threat disruption and containment capabilities delivered.4 We want to help you be one of them.
As a Microsoft partner and trusted technology advisor to many businesses like yours, we have the knowledge and expertise to get you started—as well as a variety of services and offerings that can help you stay ahead of cybercrime. Whether you need an assessment, help with licensing, or managed services, we can implement the security solution your company needs.
Get in touch by completing this form and we'll connect you with a Bulletproof expert.
4. Gartner®, Market Guide for Managed Detection and Response Services, 14 February 2023



