Detect and disrupt in-progress cyberattacks automatically
Cybersecurity attacks are getting more common and targeted. They’re also accelerating; attacks that used to take months now take days. And even the most advanced security operations teams need to take breaks to keep their organizations protected. Our cyber security experts can help you stay ahead of evolving threats.
Article Sections
The Threats Are Real
Ransomware Attacks:
Commodity and human-operated
.png?width=191&height=191&name=Processes%20(2).png)
<20 minutes from deployment to mitigate the attack.
Business Email Compromise (BEC) Attacks
Attackers pose as a trusted figure and ask recipients for payment or to share sensitive info.
.png?width=191&height=191&name=Processes%20(3).png)
81% between the first and second half of 2022.1
Adversary-in-the Middle (AitM)
An unauthorized party intercepts communication between two systems or people
.png?width=191&height=191&name=Processes%20(1).png)
100$ or less the cost of an AitM kit, which lowers the tooling and skills requires to launch an attack.2
Protect Your Business with Automatic Attack Disruption
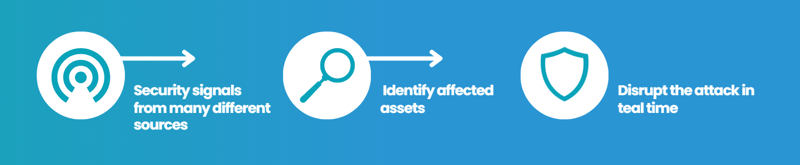
What if you could detect and disrupt an in-progress attack automatically and dramatically reduce the overall impact? As a trusted technology partner with experience in security, we can help you get this capability with extended detection and response (XDR) from Microsoft.
Why we recommend Microsoft Defender XDR
Microsoft analyzes 65 trillion signals analyzed daily and correlates them in real time across attack surfaces.3 This threat intelligence powers automatic attack disruption in Microsoft Defender XDR.
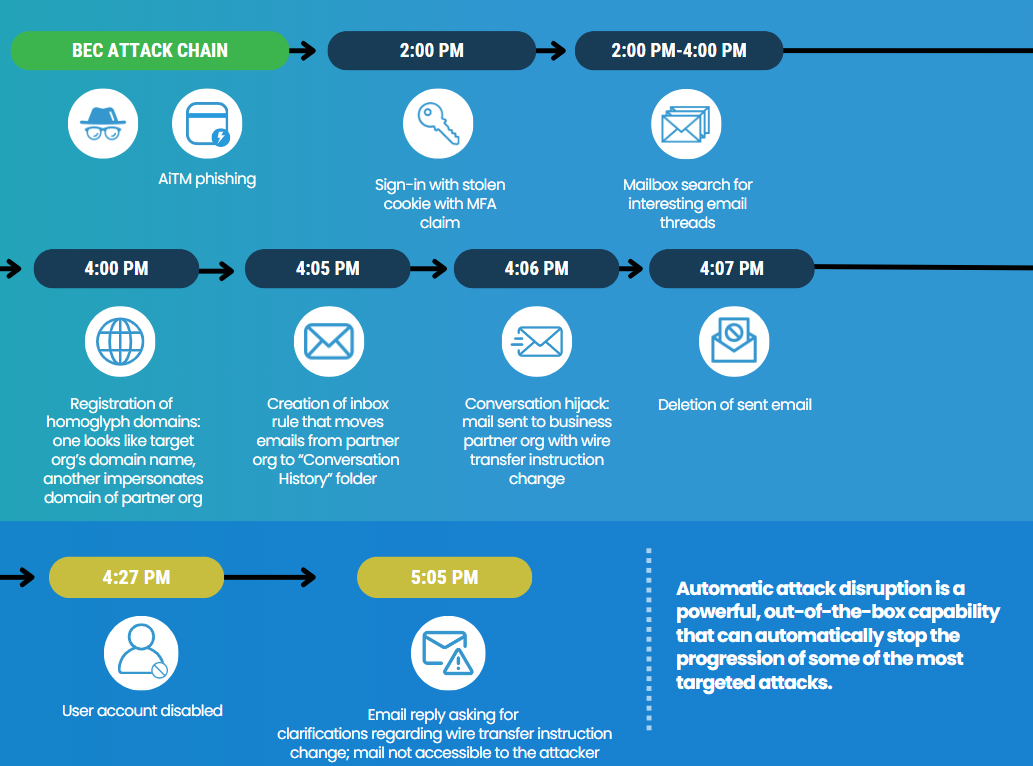
The Anatomy of a Real-Life BEC Attack
Microsoft 365 Defender used a combination of signals from identity and email security solutions—such as unfamiliar sign-in, inbox rule creation, and sending and deletion of emails—to identify the BEC attack and detect the fraud attempt.
Having established a high level of confidence through the combination of signals and alerts, Microsoft’s XDR automated actions then disabled the user account and disrupted the attack within three hours.
It prevented follow-up conversations and preventing the wire instructions from being acted upon.
Automatic Disruption: AitM Attacks
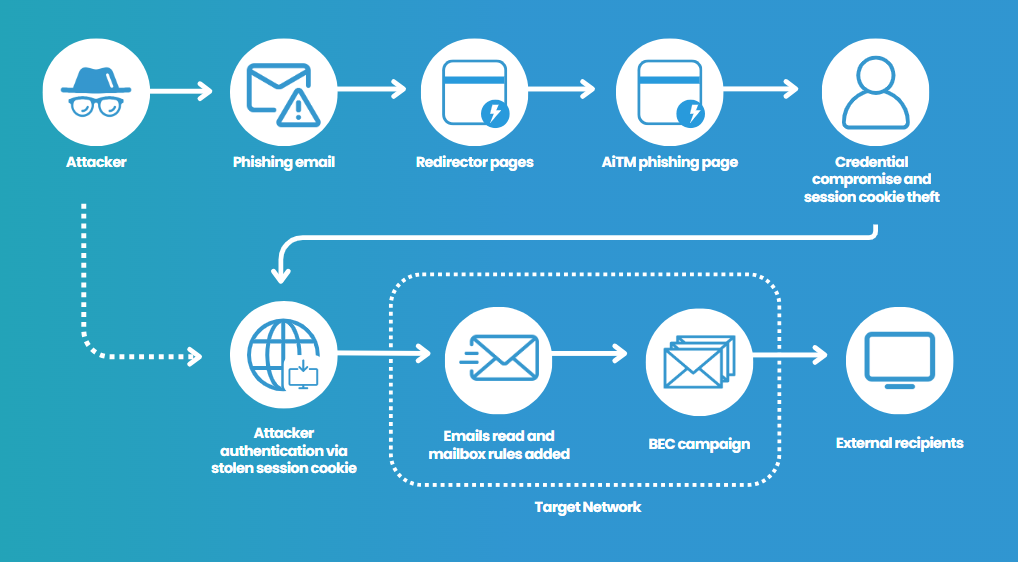
The goal of automatic disruption is to contain the attack as early as possible.
1
Identify with high confidence an AiTM attack based on multiple correlated Microsoft 365 Defender signals.
2
Automatically disable the compromised user account.
3
Automatically revoke the stolen session cookie to prevent additional malicious activity.
4
Work with the Experts

Make Your Business Immune to Disruption with Our Security Operations Center
Did you know that there are 1.7 million ransomware attacks every day? That’s 19 every second! If that number doesn’t alarm you, consider this: the average cost of a ransomware attack is a staggering $1.85 million!
That’s where our Security Operations Center (SOC) comes in. Our SOC is dedicated to serving and protecting our customers around the clock, providing 24/7 protection no matter where you are.
Watch this video for an exclusive inside look at how we keep your business secure.

Microsoft Threat Protection Envisioning Workshop
Learn how to put next-generation Microsoft security tools to work for you.
With this workshop, you’ll gain visibility into immediate threats across email, identity, and data, plus clarity and support on how to remediate vulnerabilities and upgrade your security posture for the long term.
Bulletproof Credentials
- Bulletproof named to CRN's Managed Services MSP 500 List for 2026
- Bulletproof named to CRN's Managed Services MSP 500 List for 2025
- 2025 Microsoft Intelligent Security Association Excellence Award Finalist, Security Trailblazer
- 2025 Municipal Information Systems Association BC - Associate Partner of the Year
- 2024 Microsoft Intelligent Security Association Excellence Award Winner, Security Trailblazer
- 2021 Global Security Partner of the Year Winner, Microsoft
- 5X Microsoft Canada Security IMPACT Award Winner
- 20+ years of IT, security, & compliance knowledge serving various industries across North America
- Global state-of-the-art 24/7 Security Operations Centers (SOC), 24/7 Service Desk Support, Network Operations Center (NOC), & Technology Operations Center (TOC)
-
Long-standing Microsoft Solutions Partner for Modern Work, Digital & App Innovation Azure, Infrastructure Azure, Data & AI, and Security with specializations in Cloud Security, Identity & Access Management, Data Security, and Threat Protection.
-
Member of the Microsoft Intelligent Security Association
-
Awarded General Services Administration (GSA) Multiple Award Schedule (MAS) with holder of Highly Adaptive Cybersecurity Services (HACS)
-
Certified Cybersecurity Maturity Model Certification (CMMC) Practitioner Organization

Vasu Jakkal, CVP, Microsoft Security
Get Bulletproof Expertise
By 2025, 60% of organizations will be actively using remote threat disruption and containment capabilities delivered.4 We want to help you be one of them.
As a Microsoft partner and trusted technology advisor to many businesses like yours, we have the knowledge and expertise to get you started—as well as a variety of services and offerings that can help you stay ahead of cybercrime. Whether you need an assessment, help with licensing, or managed services, we can implement the security solution your company needs.
Get in touch by completing this form and we'll connect you with a Bulletproof expert.
4. Gartner®, Market Guide for Managed Detection and Response Services, 14 February 2023




.png?width=500&height=300&name=Demio%20Resourcdes%20(500%20x%20300%20px).png)
